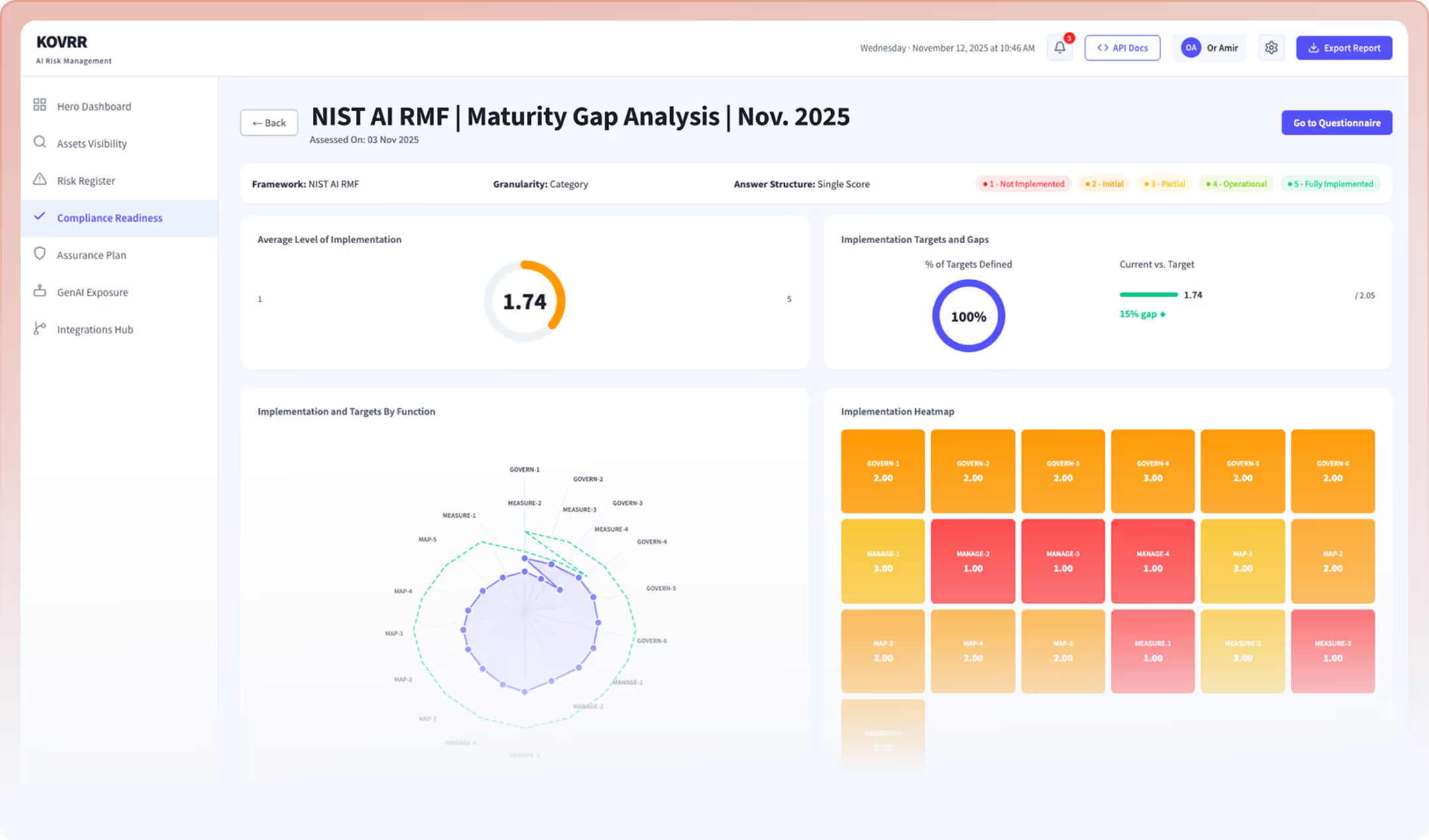
Two Frontiers. One Standard for Risk.
Redefining How Enterprises Understand, Measure, and Manage Cyber and AI Risk.

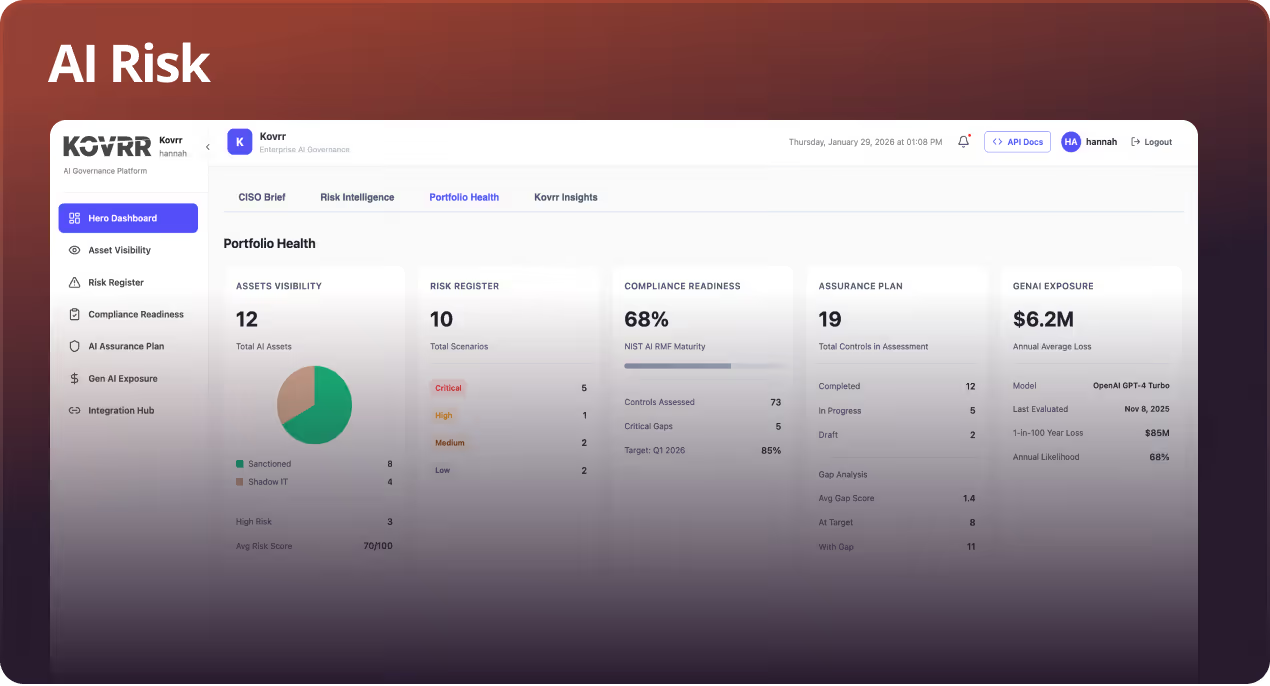
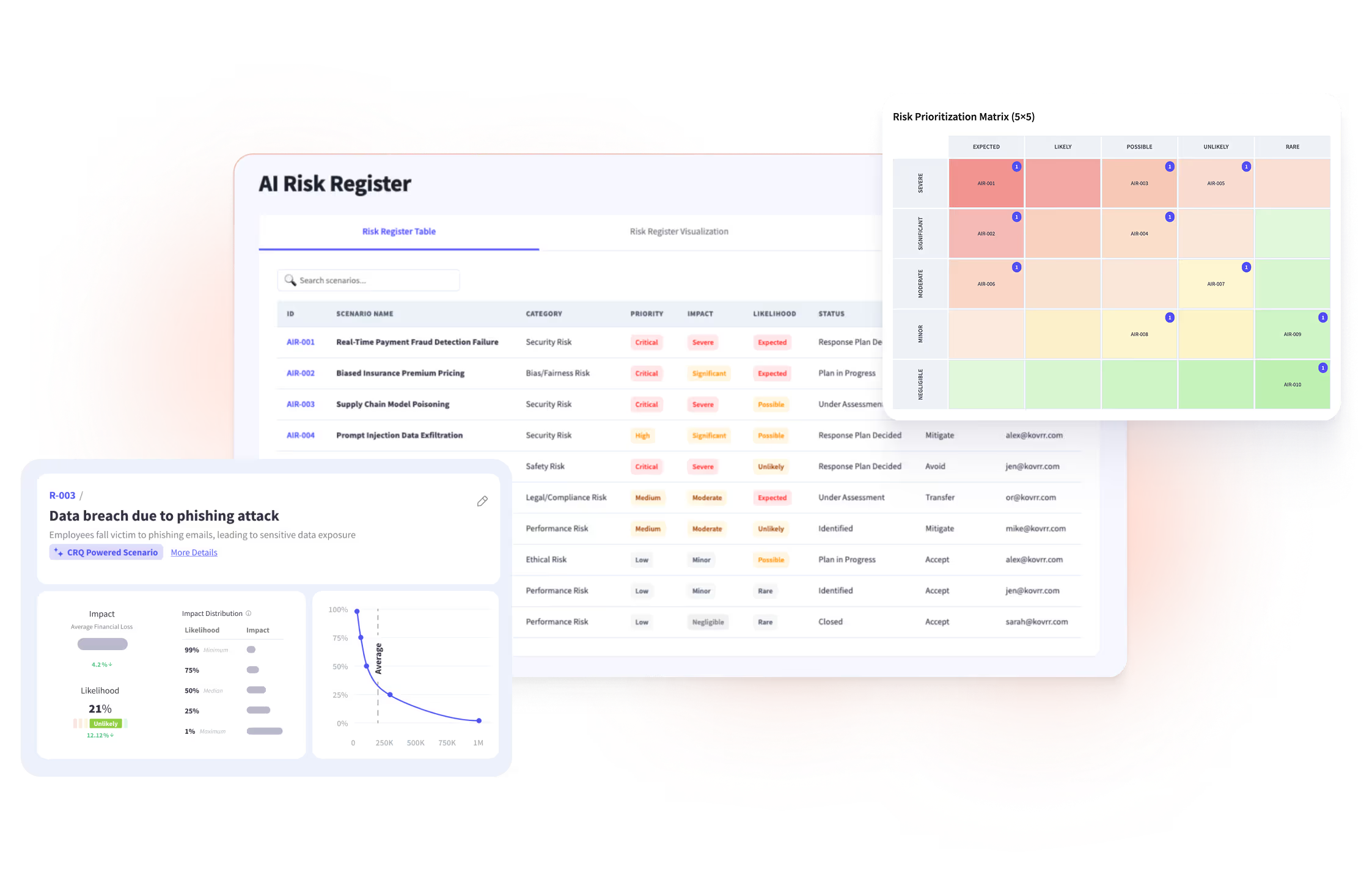
Discover Every AI Asset. Measure Every Exposure. Act on What Matters.
From visibility to governance, Kovrr delivers what professionals need to manage GenAI risk intelligently.
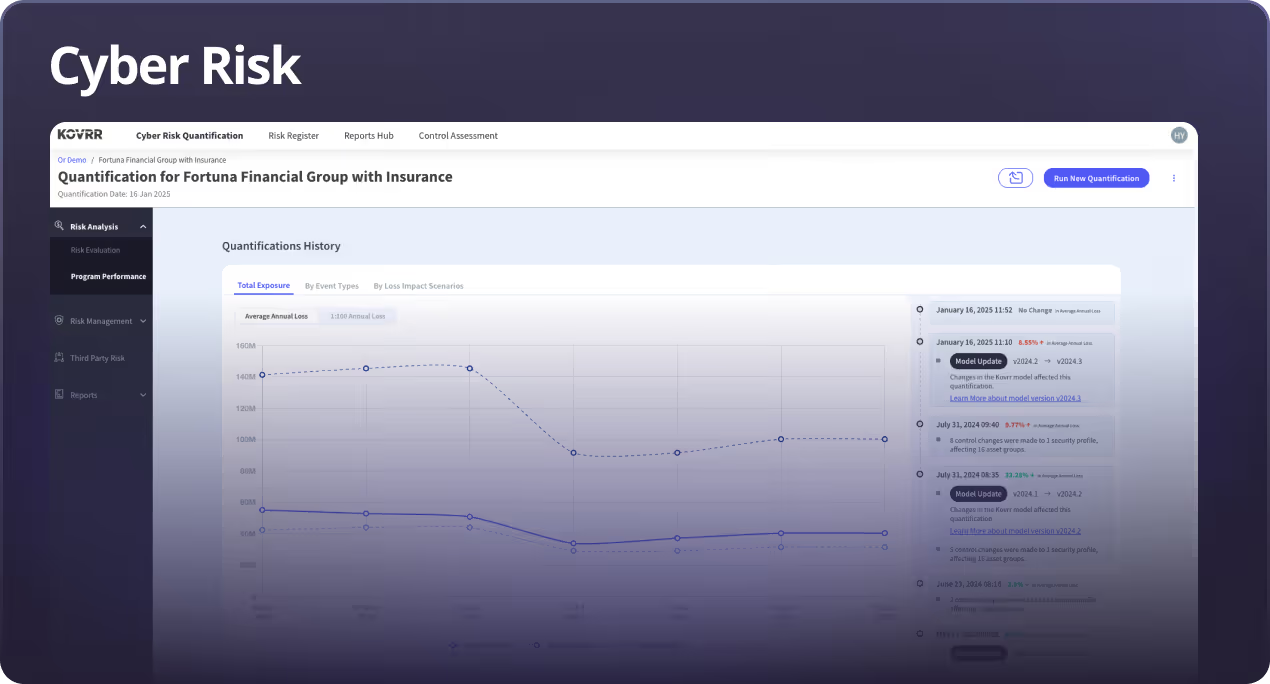
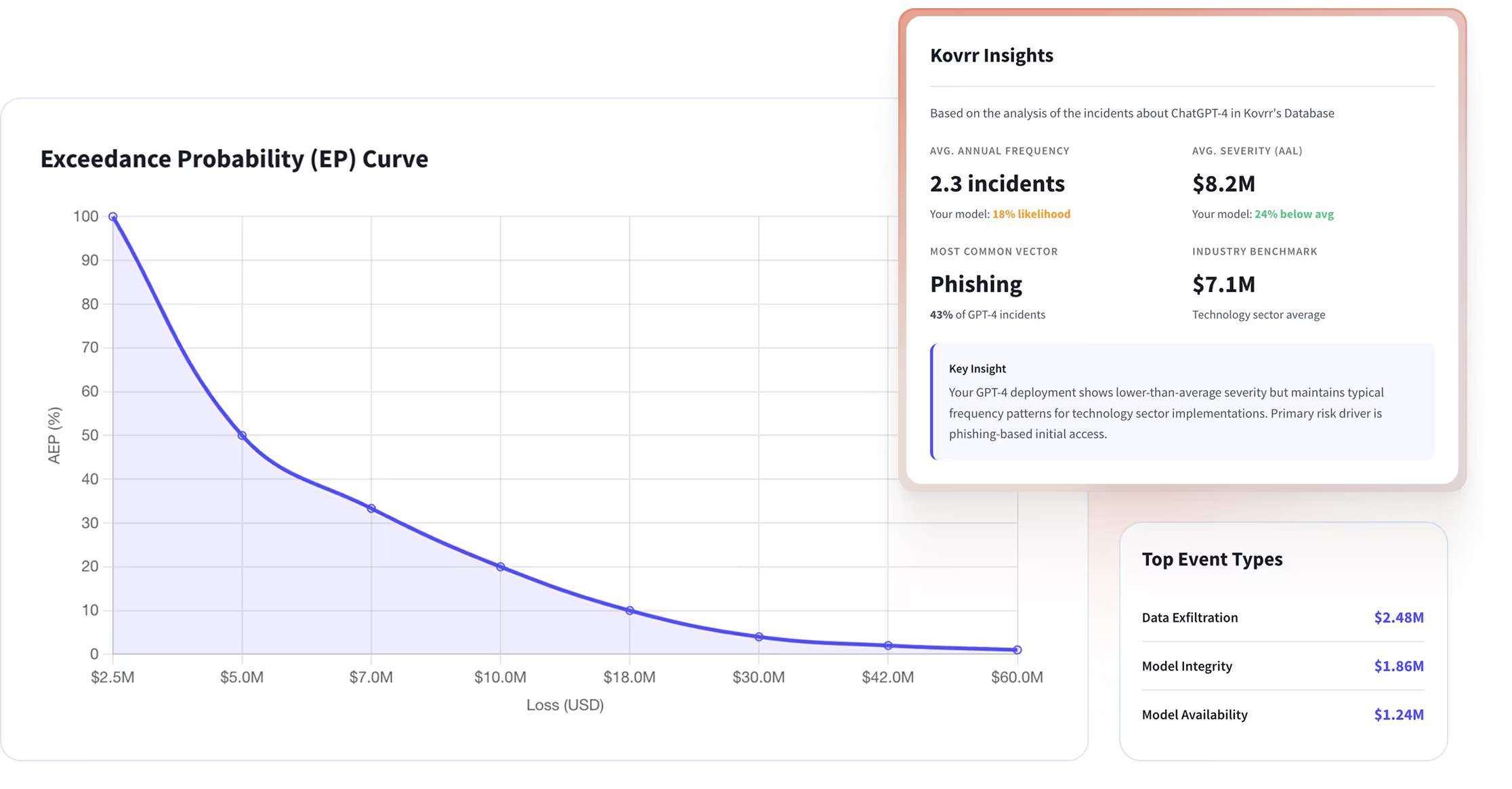
Measure Cyber Risk. Prioritize Controls. Demonstrate Impact.
Quantify exposure, maintain a dynamic risk register, and communicate tangible & defensible insights to leadership.
Trusted By Global Enterprises































Industry Frameworks
AI Regulations

- European Union: EU AI Act
- New York City: Local Law 144
- Colorado: SB 21-169
- Canada: Artificial Intelligence and Data Act (AIDA)
- UK: AI Regulation Bill
- New York State: A03779 / S00185
- Australia: Safe and Responsible AI in Australia
- NIST AI RMF
- ISO/IEC 42001
Cyber Regulations

- SEC Cybersecurity Disclosure Rules
- NYDFS Cybersecurity Regulation (23 NYCRR 500)
- HIPAA Security Rule
- The Australia Privacy Act
- Digital Operational Resilience Act (DORA)
- NIS 2 Directive
- GDPR
- Australia CPS 234
- Singapore Cybersecurity Act
- NIST CSF 2.0 (2024)
- CIS Controls (v8)
- ISO/IEC 27001