Blog Post
The Next Step in Cyber Risk Management: Decision Simulation
April 13, 2026
TL;DR
- Cyber risk management has advanced in visibility and quantification, yet organizations still lack a structured way to evaluate and justify decisions before implementation.
- Kovrr’s updated Decision Simulator enables teams to model the impact of specific actions, transforming risk management into a forward-looking process grounded in measurable financial outcomes.
- Simulations can be structured around control improvements, new security initiatives, or compliance efforts, allowing different types of decisions to be evaluated within a consistent analytical framework.
- Each scenario produces quantified results, showing how decisions influence expected loss, extreme loss scenarios, and event likelihood across multiple dimensions of exposure.
- Organizations can prioritize investments more effectively when decisions are directly tied to measurable outcomes, supporting a more disciplined and decision-driven approach to managing cyber risk.
Operationalizing Cyber Risk Decisions With Quantified Insight
At its root, cyber risk management is essentially a forward-looking discipline. The goal has never been solely to understand current exposure, but to determine which actions will reduce it most effectively, given the organization's priorities and constraints. Organizations today can assess control maturity and quantify financial exposure with increasing precision, giving security and GRC leaders a more comprehensive picture of their risk landscape than ever before. That visibility, however, has outpaced the ability to act on it.
Most organizations can identify what needs to improve. Explaining why one initiative should take priority over another, in terms that hold up to executive scrutiny, is where the process tends to collapse. When it comes to justifying investments or evaluating compliance efforts, decision-making frequently relies on assumptions rather than evidence. These are high-stakes decisions, and most organizations are making them without measurable projections to support them.
Their limitation is structural. Assessments provide a snapshot of the current cybersecurity posture at a fixed point in time. Cyber risk quantification (CRQ) translates that posture into financial terms, giving leaders a clearer sense of what is at stake. But neither process inherently offers a way to model how risk will shift in response to a specific action. Organizations are left piecing together projections manually, drawing on disconnected data sources and assumptions to estimate what a decision might accomplish.
Kovrr's significantly upgraded Decision Simulator feature brings that modeling capability directly into the quantification workflow. Security and GRC teams can model the impact of a decision long before it is implemented, whether that means improving control maturity, introducing new security capabilities, or achieving compliance with a regulatory framework. Each simulation quickly produces a quantified view of how exposure would change, replacing the manual, time-consuming process of piecing together projections with a structured, repeatable output.
Structuring and Managing Decision Scenarios
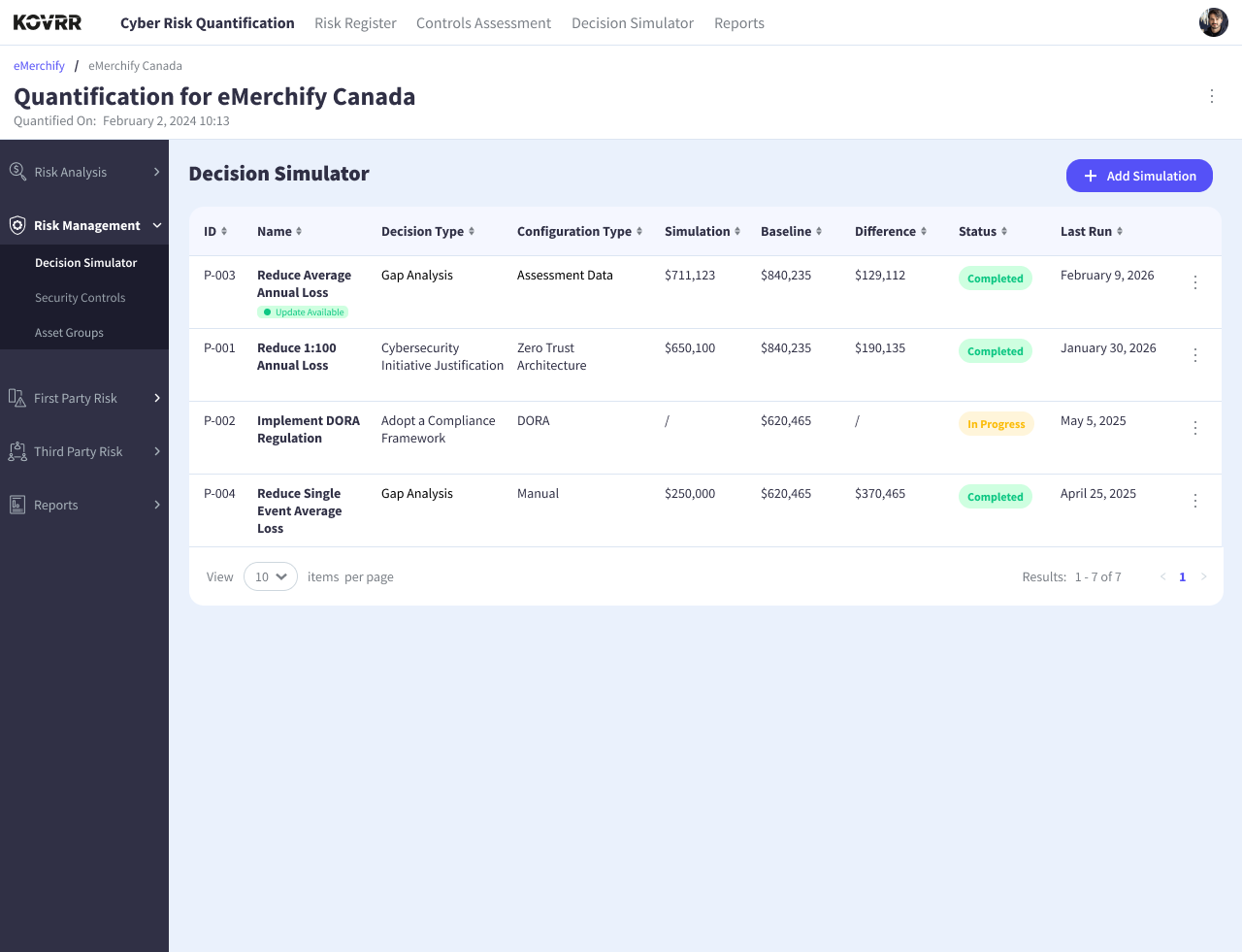
Most organizations recognize that decisions should be grounded in evidence. Putting that principle into practice consistently is where the challenge lies. Individual analyses conducted in isolation do not scale. Decisions need to be structured and comparable over time, and the teams responsible for them need a consistent environment in which to work. Accessible directly from the Risk Management tab, the Decision Simulator provides a centralized workspace where organizations can create and manage multiple decision scenarios in parallel.
The dashboard displays each simulation alongside its baseline and projected outcome, with the quantified difference between the two visible at a glance. Rather than managing separate analyses in spreadsheets or disconnected tools, security and GRC teams can maintain a living portfolio of decisions, each one tracked and evaluated against the others. Simulations can be easily revisited as new data becomes available, and the record of assumptions and outcomes remains accessible to all relevant stakeholders.
Defining the Decision: From Controls to Investments to Compliance
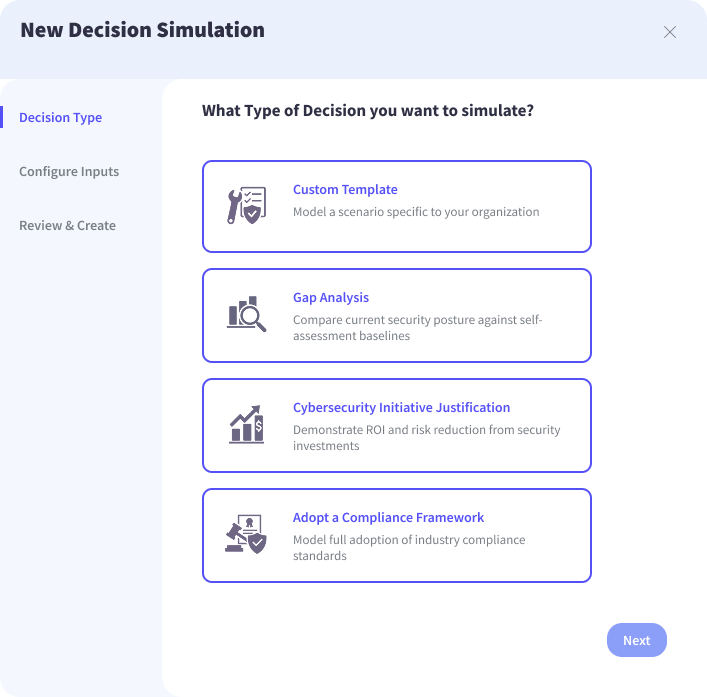
When creating a new simulation, users select from four decision types, each reflecting a distinct strategic question with its own configuration path. Clicking "Add Simulation" opens a three-step workflow that begins with the fundamental question of what type of decision needs to be evaluated. The answer determines how the simulation is configured and what inputs are required to model the outcome. The Decision Simulator currently supports four decision types, each reflecting a real strategic question that security and GRC leaders regularly face.
First, Custom Template simulations allow users to model organization-specific scenarios, providing flexibility to define and evaluate unique risk decisions beyond predefined structures. Next, Gap Analysis simulations evaluate how improving existing controls would affect overall risk exposure, drawing on current assessment data to model the impact of closing identified gaps. Cybersecurity Initiative Justification simulations model the effect of introducing new security capabilities or products, giving teams a quantified basis for evaluating whether a proposed investment is worth its cost. Finally, the Adopt a Compliance Framework simulation assesses how meeting the requirements of a specific regulatory standard would shift the organization's risk profile.
Structuring the simulator around these four decision types ensures that the platform reflects how organizations typically conceptualize risk management as a set of concrete choices with measurable consequences. Each path leads to the same standardized output, signaling that different types of decisions can be compared and prioritized using a consistent methodology. That consistency is what makes the Decision Simulator valuable as an ongoing framework for evaluating how the organization allocates its security resources over time.
Modeling Control Improvements With Real Assessment Data
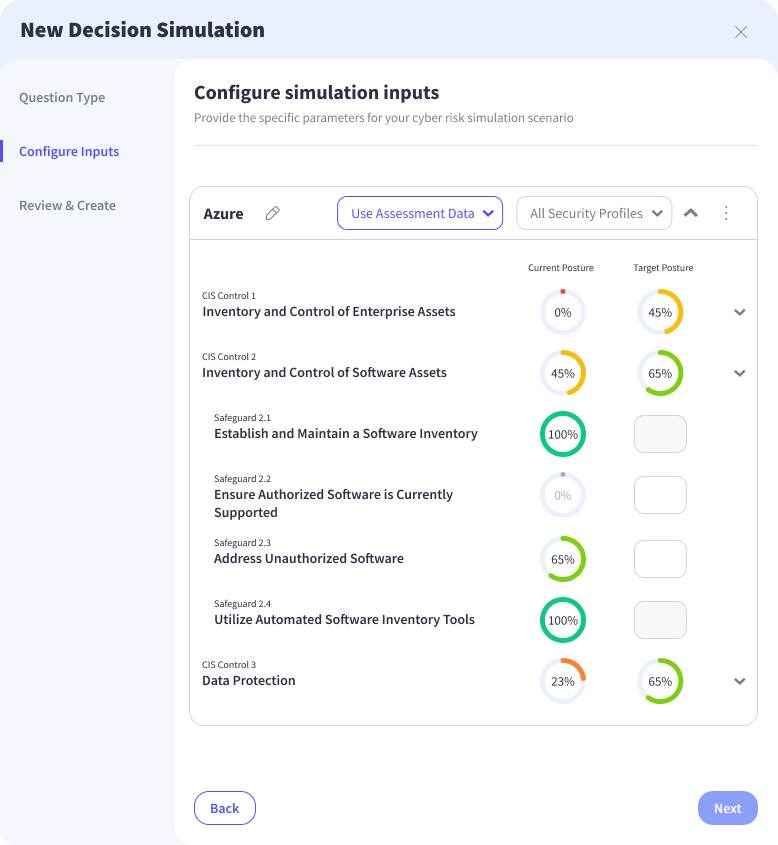
Selecting “Gap Analysis” opens the control configuration screen, where the simulation is built around the organization's actual security posture as opposed to a theoretical baseline. Current maturity levels are automatically populated from existing assessment data within the platform, ensuring that every scenario begins from an accurate, up-to-date picture of how controls are implemented across the environment. From there, users define a target state by setting maturity levels for each control.
Targets can be drawn directly from prior control assessment results, keeping the simulation aligned with established GRC processes, or entered manually to model hypothetical improvements or exploratory scenarios. The screenshot above shows this configuration at the control and safeguard level, with current posture on the left and target posture on the right, giving users a precise, granular view of exactly what is being changed and by how much.
Simulations can be scoped to specific assets or business units, which matters considerably for organizations with multiple subsidiaries, regions, or operational environments. Control maturity rarely looks the same across an entire enterprise, and modeling improvements at that level of granularity produces results that are far more accurate and actionable than aggregated assumptions would allow. The final outputs connect those projected control improvements directly to financial impact.
Evaluating Security Investments Through Quantified Impact
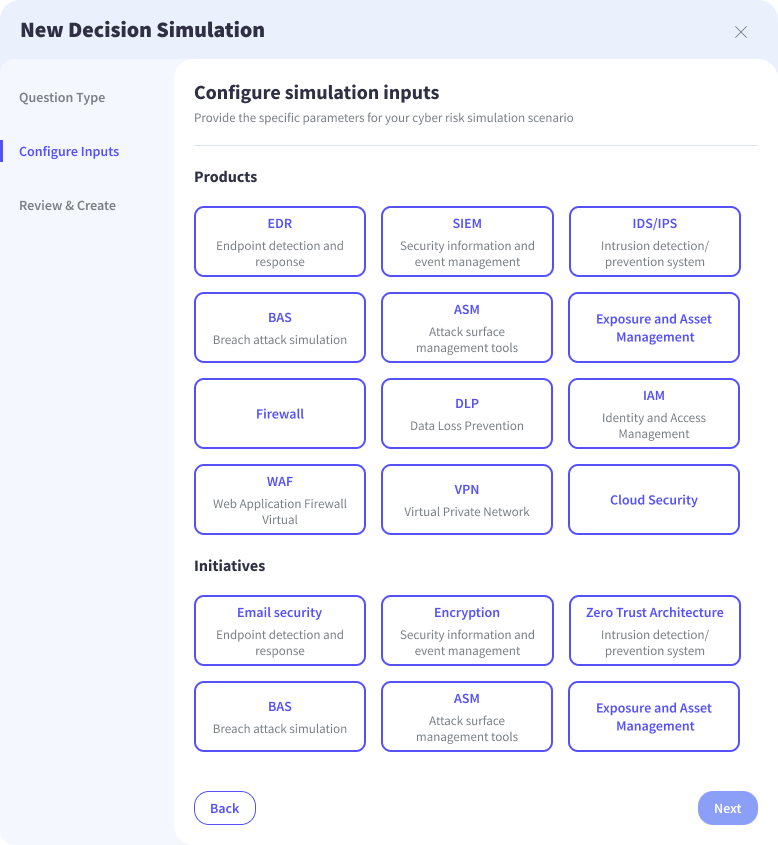
While improving existing controls addresses known gaps, organizations are equally required to make forward-looking investment decisions. These decisions often involve introducing new security capabilities, yet are frequently evaluated without a clear understanding of how they will influence overall risk exposure. As a result, investment planning tends to rely on assumptions or external pressure instead of on a more structured and objective assessment of measurable impact.
The Decision Simulator enables teams to model these investments directly through a set of standardized security capabilities and initiatives. Users define the type of capability being introduced, allowing each scenario to remain consistent and comparable within the broader risk model. Each selected capability is then systematically mapped to the controls it strengthens, creating a direct relationship between investment decisions and changes in security posture, ensuring that simulations reflect how improvements materialize at the control level.
The platform evaluates how these capabilities reshape the underlying structure of risk. By translating these changes into quantified outcomes, the platform provides a clear view of how an investment alters exposure before it is implemented. Resource allocation can then be guided by evidence, ensuring that investment decisions are grounded in demonstrable outcomes rather than indirect reasoning.
Simulating the Impact of Compliance on Risk Exposure
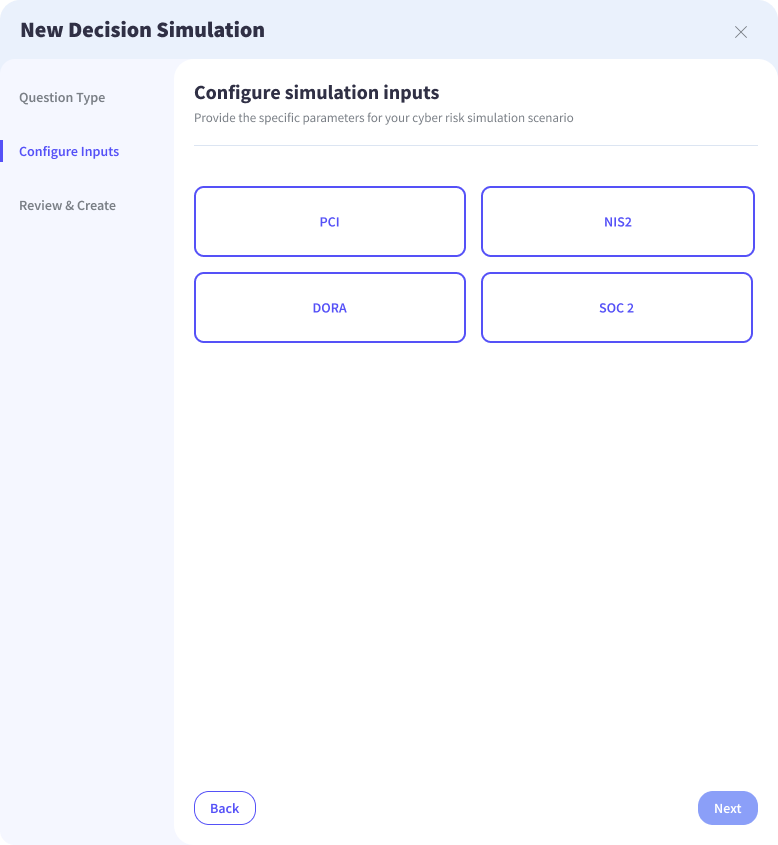
Regulatory compliance is often approached as a discrete requirement, operating alongside risk management. Although organizations often invest significant effort in meeting framework obligations, the relationship between compliance and risk reduction is rarely made explicit. Consequently, it remains unclear whether achieving compliance meaningfully improves the organization’s overall risk posture. The Decision Simulator brings these domains into alignment by modeling compliance as a measurable shift in control maturity.
Users select from established cybersecurity frameworks such as NIS2, DORA, PCI, and SOC 2, each translated into a defined set of control requirements within the platform. Target maturity levels are calibrated to reflect achievable compliance standards, allowing the model to capture the actual effort required to meet regulatory expectations. Kovrr extends beyond predefined frameworks through direct mapping of additional regulatory requirements to relevant controls within the platform.
Given the customization options, compliance simulations can remain aligned with organization-specific obligations and evolving regulatory demands. A clearcut association is therefore established between compliance efforts and quantified risk outcomes, ensuring regulatory alignment is no longer treated as a binary milestone, but as a measurable shift in exposure across different scenarios, as well as a strategic lever within broader risk management decisions.
Translating Decisions Into Measurable Risk Reduction
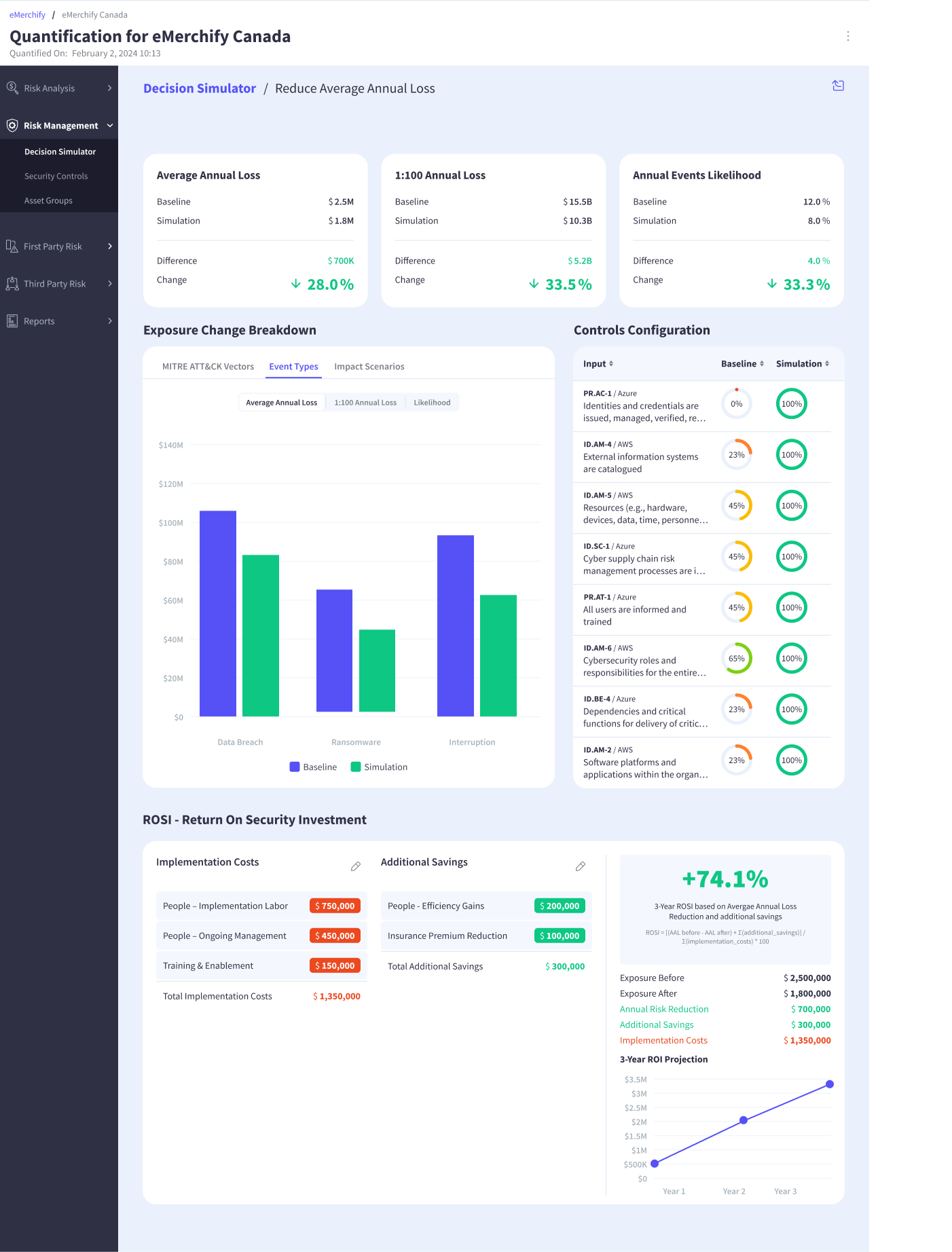
Once a simulation is executed, results are presented through a structured and consistent analytical layer. Each modeled decision is translated into measurable changes in risk, allowing baseline values to be evaluated directly against simulated outcomes. The comparison highlights how exposure shifts as a result of specific actions, making the impact of each decision explicit. A clear connection is established between the scenario being modeled and its financial implications, including both risk reduction and investment return, ensuring that results can be interpreted within a broader risk management context.
Quantifying the Impact on Financial Risk

Core risk metrics capture both expected and extreme loss scenarios, providing a comprehensive view of exposure. Average Annual Loss represents expected financial impact over time, while the 1:100 loss reflects potential high-severity events. Annual event likelihood adds further context by indicating how frequently these events may occur. Baseline and simulated values are displayed side by side, allowing changes to be evaluated based on how they alter both the probability and magnitude of loss.
Understanding Where Exposure Changes Occur

A detailed breakdown of exposure reveals how risk shifts across different dimensions. Loss is segmented by event types such as data breach, ransomware, and operational interruption, providing visibility into how specific scenarios are affected. Additional perspectives, including MITRE ATT&CK vectors and impact scenarios, extend the analysis by linking exposure changes to underlying threat patterns and business consequences. Greater granularity allows organizations to identify where risk is meaningfully reduced, as well as where it persists.
Tracing Risk Reduction Back to Control Changes

Control-level visibility connects changes in exposure to the mechanisms driving them. Baseline and simulated control maturity levels are presented in parallel, making it possible to observe how specific adjustments influence overall risk. Indirect changes, such as those introduced through new initiatives or compliance requirements, are translated into clear control improvements within the model. The result is a transparent view of how decisions produce outcomes, enabling stakeholders to understand the underlying drivers of risk reduction.
Evaluating Return on Security Investment (ROSI)

The ROSI view extends the analysis by incorporating the financial inputs required to achieve it. Implementation costs, including labor, ongoing management, and enablement, are defined alongside additional savings such as efficiency gains and insurance premium reductions. These inputs are combined with quantified risk reduction to calculate overall return, expressed as a percentage over a defined time horizon. The result is a more complete view of impact, allowing security investments to be evaluated with the same level of rigor as other business decisions.
From Quantification to Decision-Driven Risk Management
Cyber risk management has traditionally centered on visibility into exposure, supported by assessments and maturity scoring. But the growing expectation placed on security and risk leaders now extends that mandate further, requiring clear justification for how it is reduced and why specific decisions are made. Decision simulation introduces a more disciplined approach to that challenge.
Future actions can be evaluated before implementation, with outcomes expressed in financial terms and grounded in modeled exposure. The focus subsequently shifts toward understanding the consequences of change, allowing decisions to be examined through their projected impact as opposed to the inferred benefit. Kovrr’s Decision Simulator embeds this approach within a single analytical framework.
Control improvements, security initiatives, compliance efforts, and organization-specific scenarios can all be evaluated using the same structure, ensuring consistency across different types of decisions. Connecting quantified risk reduction with the financial inputs required to achieve it gives organizations a clearer view of both impact and return. As risk environments continue to evolve, the ability to connect insight with action becomes increasingly important. Decision simulation establishes that connection.
Organizations looking to connect risk insight with actionable decision-making can explore Kovrr’s Decision Simulator in practice. Schedule a demo today with one of Kovrr’s cyber risk experts to see how decisions can be modeled and measured.



.webp)